Whitelisting an IP Address for Penetration Testing in Cloudflare
Getting ready to run a web application penetration test? Don't forget to whitelist your tester's IP address in your WAF. It might seem counterintuitive, but it helps make sure your consultant's time is used efficiently, giving you the best results.

I can hear some of you already.
"True security testing should mimic real-world conditions as closely as possible. It's like telling your kids where you hid the cookies and then acting surprised they found them. Are we really testing our security, or just playing pretend?" - John Doe, Director of IT - ACME Corp
While John's right that it might not make for the most realistic test of a given web application, realism often isn't the only goal. In code assisted tests, sometimes it's not a goal at all.
The primary goal should be to identify vulnerabilities in your web application caused by your code, misconfigurations in your infrastructure, or seeing if we can chain several of these issues together. Testing with a WAF (Web Application Firewall) in place can hinder this process.
- Testing Efficiency
WAFs affect testing efficiency, for example, rate limiting rules slow down the rate at which a tester can issue requests to the web application.
Since penetration tests are often conducted within a limited timeframe, any increase in the time needed to complete the test directly influences the cost incurred by you. - Accuracy of Vulnerability Detection
WAF's can conceal vulnerabilities in your code base. By filtering out or blocking malicious attempts and patterns, a WAF might prevent the penetration tester from uncovering weak spots in your application.
If the WAF were to become non-operational or if a bypass were discovered at a later point in time, this situation would reveal the underlying vulnerability leaving you exposed.
Our Recommendation
But what if you want to validate your WAF is actually working? We hear you.
Our recommendation is that the testing be conducted with the WAF disabled for the tester. Once the testing phase is completed, and vulnerabilities have been identified we can attempt exploitation again with the WAF re-enabled OR attempt exploitation from a separate IP.
Cloudflare WAF Whitelisting Steps (October 2025)
Here are the steps to whitelist an IP address from Cloudflare's WAF.
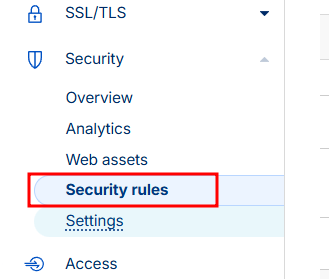
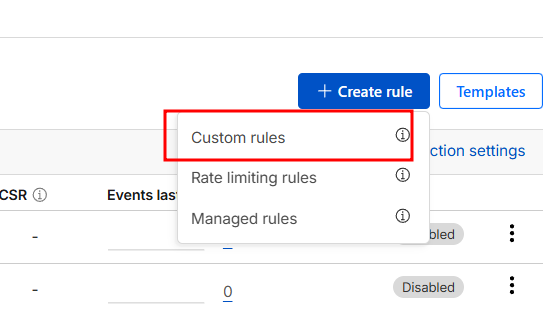
Create a custom rule.
Give the rule a name, and configure the rule to match if the Source IP address is a given value.
Take the action of 'Skip' and ensure you click all components including those under the 'More components' dropdown.
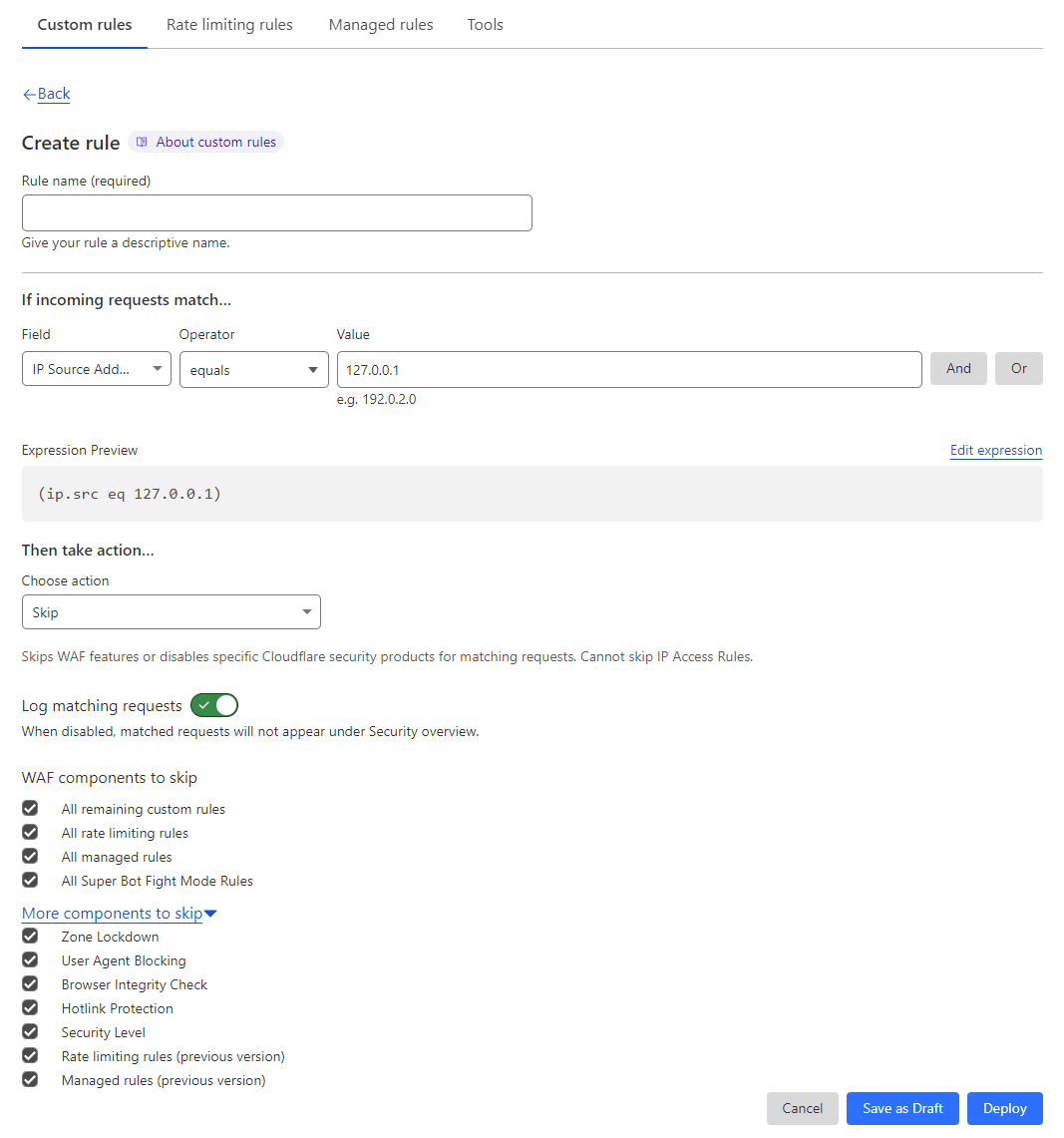
Click the Deploy button and you're done!

