Set ms-DS-MachineAccountQuota to 0
By default, low privileged users can create up to 10 computer accounts in an Active Directory domain. Unless you regularly have end users joining computers to the domain, it should be set to 0.
In the internal network penetration tests we conduct, we routinely leverage the default MachineAccountQuota to gain persistent, authenticated access to an Active Directory domain.
In many instances, we are able to coerce authentication from a low-privileged user and relay this to create a computer account for which we have the password. Without this, we would be limited to the victim's permissions on the relayed host (often none), or be forced to attempt to crack the victim's password (not always feasible).
By setting the quota to 0, only Domain Admins or those with delegated permissions will be able to join new computers to the domain.
Note, this doesn't impact end users joining computers to Intune/Entra via Autopilot as Entra devices have nothing to do with computer objects in an on-premises domain.
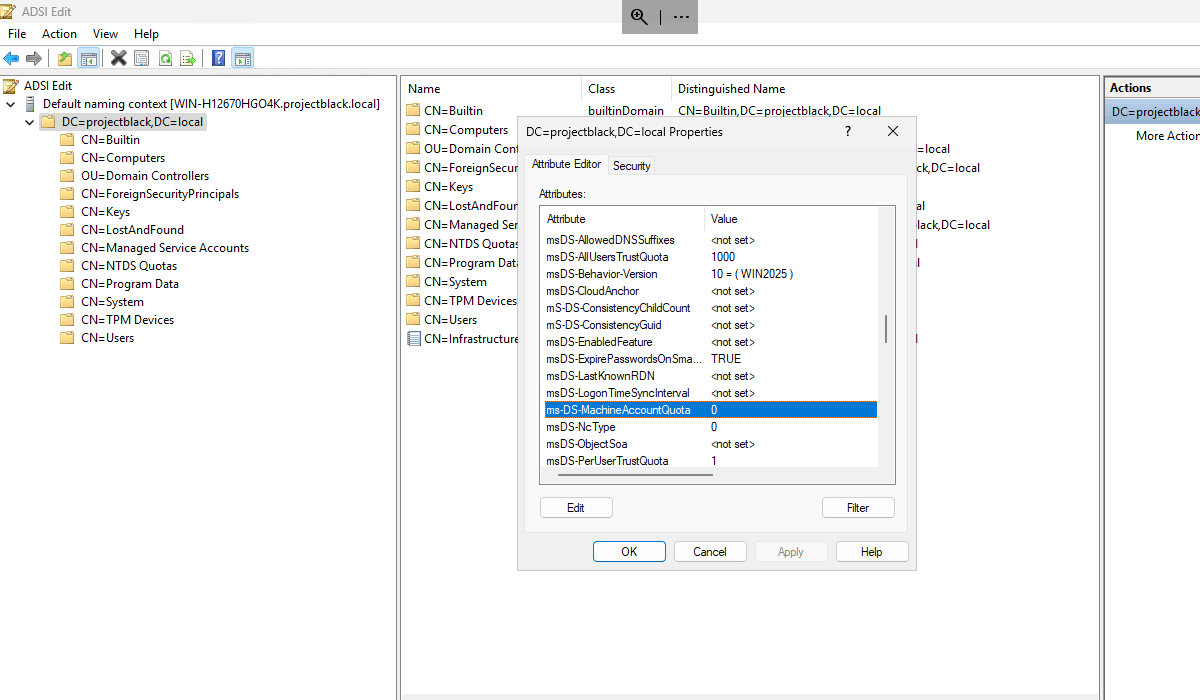
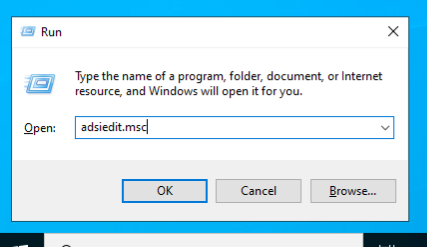
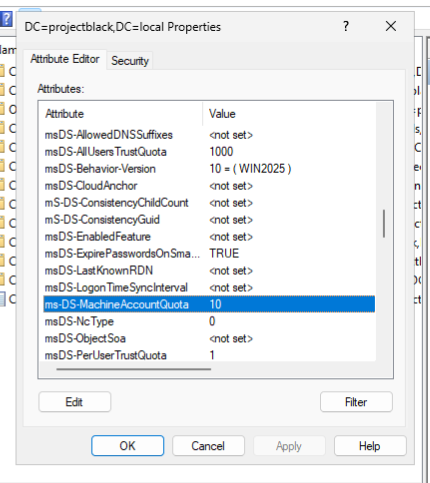
ADSI Edit
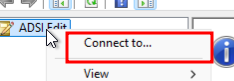
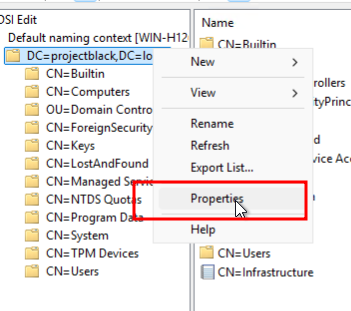
Launch ADSI Edit and connect to the Default naming context.
Open Properties and find the ms-DS-MachineAccountQuota. Set this to 0.
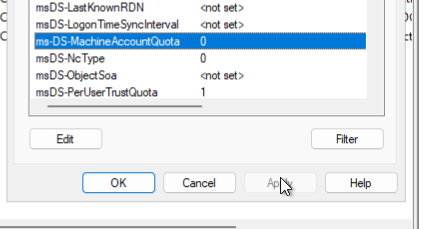
Done.
Powershell
To query the current Quota:
Get-ADObject ((Get-ADDomain).distinguishedname) -Properties ms-DS-MachineAccountQuotaTo set it to 0:
Set-ADDomain -Identity (Get-ADDomain).distinguishedname -Replace @{"ms-DS-MachineAccountQuota"=0}Retrospectively Investigate
We can also check to see if someone in your AD domain has already abused this or has been joining their own computers to the domain.
When an unprivileged account that's not a Domain Admin creates a computer account, the computer account will have the mS-DS-CreatorSID set to the creator's account SID. We can query this and resolve this to a human readable account name to identify any suspicious activity.
Get-ADComputer -Filter 'mS-DS-CreatorSID -like "*"' -Properties mS-DS-CreatorSID | Select-Object Name, @{N='CreatedBy';E={(New-Object System.Security.Principal.SecurityIdentifier($($_."mS-DS-CreatorSID"))).Translate([System.Security.Principal.NTAccount]).Value}}It looks like alice has been up to something in our lab.
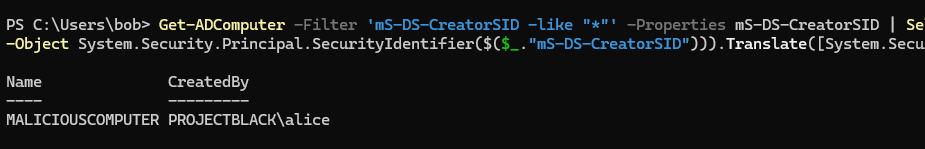
If you get no output then there are currently no computer accounts that have been created by low privilege users .

