Fixing ESC4 - User has dangerous permissions.
Prevent ESC4 ADCS attacks by restricting permissions assigned to users and groups.
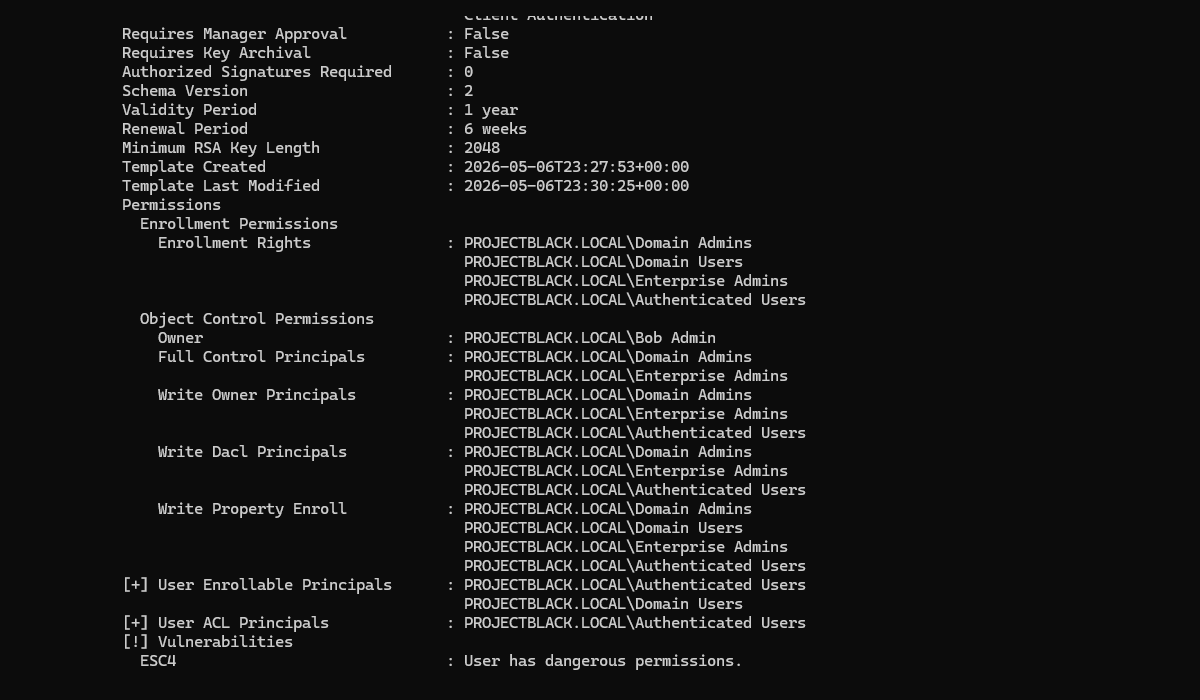
The ESC4 misconfiguration is also commonly referred to as certificate template hijacking or vulnerable/weak certificate template ACLs.
The fundamentals of this attack are relatively simple: as a low privileged user if we can can modify a certificate template's settings, then we can reconfigure it to be vulnerable in a different way that allows us to receive a certificate for a higher privileged user. Penetration testers and threat actors can then revert their configuration changes before anyone notices.
Your certificate template is vulnerable if any of the following permissions are assigned to a lower privileged user - Table source.
| Right | Description |
|---|---|
Owner | The principal has implicit full control of the object and can edit any property. |
Full Control | The principal has full control of the object and can edit any property. |
Write Property | The principal has generic write on the object and can edit any property. |
Write Owner | The principal can change the owner of the object. |
Write Dacl | The principal can modify the access controls of the object. |
The Fix
Fortunately, the fix is extremely simple.
Check the security tab of the vulnerable certificate template and look for low privileged groups or users that have been assigned any permissions from the table above.
In our example, all Authenticated Users have been assigned the Write (Write Property) permission over a certificate template.
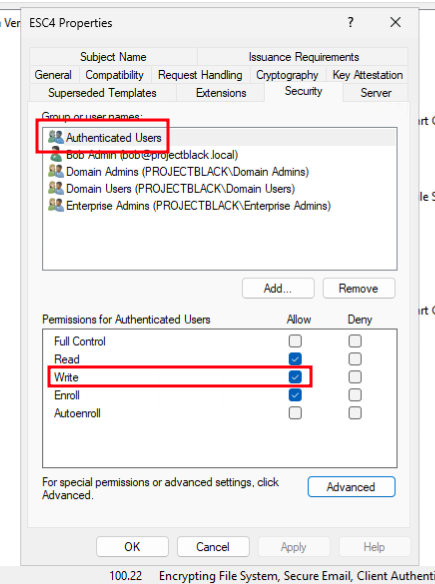
Untick the offending write permission and this privilege escalation path is resolved.

